When it comes to cybersecurity, macOS is seen by many as a role model. Some Apple fans might even view their fruit-labeled computer as immune to attacks by cybercriminals, with Apple itself considering built-in macOS security measures adequate for the threats targeting it. But is it really bulletproof?
The SolarWinds supply-chain attack, vulnerabilities in Microsoft Exchange and countless ransomware incidents are just some of the most prominent cyberattacks that made headlines in the early part of 2021. And new ones appear almost daily. There is one thing all of them have in common: the security problems usually concern Microsoft systems. Compared to that, Apple’s macOS pops up only in a handful of cases each year.
This may be due to the fact that Windows remains the most used operating system on corporate endpoints and servers. Nevertheless, Apple has been slowly but steadily increasing its market share, and as the number of devices using Apple operating systems rises, so does the interest of cybercriminals.
In business environments, Macs are popular among creative professionals such as graphic designers and video creators, and in desktop publishing. For personal use, MacBooks or iMacs may be preferred due to the intuitive and user-friendly interface of the operating system and applications and their high-end design.
But how secure is macOS? Let’s take a closer look.
Popular belief #1: There’s no malware for macOS
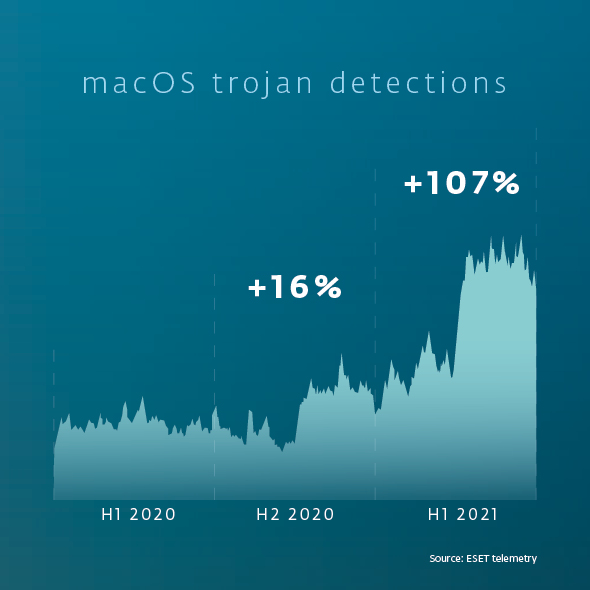
This is definitely not true. There are thousands of malware families targeting macOS. ESET telemetry shows tens of thousands of trojan detection events globally throughout 2020, with a significant uptick in activity since the last quarter of 2020.
What are the other popular beliefs about macOS cybersecurity?
“MacOS is secure by design.”
“Those few vulnerabilities don’t mean anything.”
“Hackers are not interested in Apple.”
“Macs don’t need a security solution.”
Which of them are correct, and which are just dangerous misconceptions? Find out in the free e-book by ESET.